
หลักสูตรเทคนิคการสืบสวนสอบสวนการทุจริตทางดิจิทัล หลักสูตร 2 วัน

- ระยะเวลา: 2 วัน (09:00 – 16:00 น.)
- รูปแบบการเรียน: การบรรยาย + เวิร์กชอปเชิงปฏิบัติการ
- อุปกรณ์ที่จัดเตรียมให้: ซอฟต์แวร์สำหรับฝึกอบรม , ชุดข้อมูล (Datasets) และพยานหลักฐานจำลอง (Investigation Artifacts) และ Demo Mobile Device Forensics Accessories
ภาพรวมหลักสูตร
การทุจริตทางดิจิทัล, การโจรกรรมข้อมูล, ภัยคุกคามจากคนใน และการละเมิดทรัพย์สินทางปัญญา ถือเป็นความเสี่ยงที่สำคัญที่สุดประการหนึ่งที่องค์กรสมัยใหม่ต้องเผชิญ การสืบสวนเหตุการณ์เหล่านี้อย่างมีประสิทธิภาพจำเป็นต้องมีระเบียบวิธีทางนิติวิทยาศาสตร์ที่เป็นระบบ การจัดการพยานหลักฐานที่เหมาะสม และความรู้ด้านข้อกำหนดทางกฎหมายเพื่อให้พยานหลักฐานเป็นที่ยอมรับในชั้นศาล
หลักสูตรเทคนิคการสืบสวนสอบสวนการทุจริตทางดิจิทัลนี้ มุ่งเน้นให้ผู้เข้าอบรมได้รับความรู้เชิงปฏิบัติและทักษะที่จำเป็นในการระบุ เก็บรวมรวม วิเคราะห์ และรายงานพยานหลักฐานดิจิทัลที่เกี่ยวข้องกับการทุจริตและการรั่วไหลของข้อมูล
เนื้อหาหลักสูตรเป็นการผสมผสานระหว่างพื้นฐานทางทฤษฎี กรณีศึกษาจากเหตุการณ์จริง และการฝึกปฏิบัติโดยใช้ชุดข้อมูลและหลักฐานจำลองที่พบได้บ่อยในการสืบสวนจริง โดยระเบียบวิธีฝึกอบรมอ้างอิงตามแนวทางปฏิบัติที่ดีที่สุด (Best Practices) ซึ่งเป็นที่ยอมรับในระดับสากลจากองค์กรต่างๆ เช่น:
- สถาบันมาตรฐานและเทคโนโลยีแห่งชาติ (NIST)
- องค์การระหว่างประเทศว่าด้วยการมาตรฐาน (ISO/IEC)
- Association of Chief Police Officers (ACPO)
วัตถุประสงค์ของหลักสูตร
เมื่อสิ้นสุดการอบรม ผู้เข้าอบรมจะสามารถ:
- เข้าใจพื้นฐานด้านนิติวิทยาศาสตร์ดิจิทัลและการสืบสวนการทุจริต
- ระบุแหล่งพยานหลักฐานดิจิทัลที่อาจเกิดขึ้นได้ในระหว่างการสืบสวน
- ตรวจยึดและรักษาพยานหลักฐานดิจิทัลอย่างถูกต้องตามมาตรฐานนิติวิทยาศาสตร์
- กู้คืนข้อมูลที่ถูกลบหรือถูกซ่อนจากระบบดิจิทัล
- วิเคราะห์ข้อมูลเมทาดาตา (Metadata) ของไฟล์และร่องรอยบนระบบ (System Artifacts)
- ตรวจสอบเทคนิคการต่อต้านนิติวิทยาศาสตร์ (Anti-forensic) ที่ใช้เพื่อซ่อนพยานหลักฐาน
- สืบสวนภัยคุกคามจากคนใน(Insider Threat) และเหตุการณ์ข้อมูลรั่วไหล
- วิเคราะห์ไฟล์เหตุการณ์ (Log files) และลำดับเหตุการณ์ (Event Timeline)
- สืบสวนกรณีการทุจริตในองค์กรและการละเมิดทรัพย์สินทางปัญญา
- ดำเนินการสืบสวนนิติวิทยาศาสตร์บนอุปกรณ์เคลื่อนที่ (Mobile Forensics) เบื้องต้น
- จัดทำรายงานการสืบสวนที่เหมาะสมสำหรับกระบวนการทางกฎหมาย
- นำเสนอพยานหลักฐานดิจิทัลในชั้นศาลในฐานะพยานผู้เชี่ยวชาญ (Expert Witness)
ผู้ที่ควรเข้ารับการอบรม
หลักสูตรนี้ออกแบบมาสำหรับผู้เชี่ยวชาญที่เกี่ยวข้องกับการสืบสวน, ความมั่นคงปลอดภัยไซเบอร์, การกำกับดูแล (Compliance) และการป้องกันการทุจริต ได้แก่:
- ผู้สืบสวนการทุจริต (Fraud Investigators)
- ผู้ตรวจสอบภายใน (Internal Auditors)
- เจ้าหน้าที่กำกับดูแลการปฏิบัติงาน (Compliance Officers)
- นักวิเคราะห์ความมั่นคงปลอดภัยไซเบอร์ (Cybersecurity Analysts)
- นักนิติวิทยาศาสตร์ดิจิทัล (Digital Forensics Investigators)
- เจ้าหน้าที่บังคับใช้กฎหมาย (Law Enforcement Officers)
- นักกฎหมายที่เกี่ยวข้องกับคดีอาชญากรรมทางไซเบอร์
- บุคลากรด้านความปลอดภัยไอที (IT Security Personnel)
- ผู้เชี่ยวชาญด้านการบริหารจัดการความเสี่ยง (Risk Management Professionals)
คุณสมบัติและสิ่งที่ต้องเตรียมของผู้เข้าอบรม
- ทักษะพื้นฐานในการใช้งานคอมพิวเตอร์
- ความเข้าใจพื้นฐานเกี่ยวกับระบบไอทีหรือความมั่นคงปลอดภัยไซเบอร์ (แนะนำแต่ไม่บังคับ)
- คอมพิวเตอร์โน้ตบุ๊ก (ไม่บังคับ หากมีการจัดเตรียมอุปกรณ์ในแล็บให้)
- มีความสนใจในการสืบสวนดิจิทัลหรือการตรวจจับการทุจริต
หัวข้อการเรียนรู้ (Course Modules)
- บทนำสู่นิติวิทยาศาสตร์ดิจิทัล (Introduction to Digital Forensics)
- การระบุและตรวจยึดอุปกรณ์ดิจิทัลอย่างถูกต้อง (Identification & Seizure of Digital Equipment)
- ความสมบูรณ์และการรับฟังพยานหลักฐานดิจิทัลตามกฎหมาย (Legal Admissibility of Digital Evidence)
- การกู้คืนและการวิเคราะห์ข้อมูลพยานหลักฐาน (Data Recovery & Analysis)
- เทคนิคการตรวจสอบการต่อต้านนิติวิทยาศาสตร์ (Anti-Forensics Techniques)
- การตรวจสอบข้อมูลเมทาดาตา (Metadata Examination)
- การวิเคราะห์ไฟล์เหตุการณ์ (Log File Analysis)
- การสืบสวนภัยคุกคามจากคนในและการรั่วไหลของข้อมูล (Insider Threat & Data Leak Investigation)
- การสืบสวนการทุจริตในองค์กร การเงิน และการละเมิดทรัพย์สินทางปัญญา (Corporate & Financial Fraud & Intellectual property infringement)
- การสืบสวนนิติวิทยาศาสตร์บนอุปกรณ์เคลื่อนที่ (Mobile Forensics Investigation)
- กระบวนการเบิกความและนำเสนอพยานหลักฐานในชั้นศาล (Testifying in Court)
- เทคนิคการเขียนรายงานผลการสืบสวนสอบสวน (Investigation Report Writing)
📅 ตารางการอบรม Day 1: Technical Core & Evidence Foundations
วัตถุประสงค์: เน้นการเก็บกู้และวิเคราะห์ร่องรอยดิจิทัลพื้นฐานตามหลักการ Forensic
| เวลา | หัวข้อหลัก | รายละเอียดและมาตรฐานที่เกี่ยวข้อง |
| 09:00 – 10:30 | บทนำสู่นิติวิทยาศาสตร์ดิจิทัล (Introduction to Digital Forensics) | มาตรฐาน ACPO (4 Principles), ISO/IEC 27037 * กฎการรักษาความถูกต้องของหลักฐาน (Chain of Custody) การระบุและตรวจยึดอุปกรณ์ดิจิทัลอย่างถูกต้อง (Identification & Seizure of Digital Equipment) ความสมบูรณ์และการรับฟังพยานหลักฐานดิจิทัลตามกฎหมาย (Legal Admissibility of Digital Evidence) |
| 10:45 – 12:00 | Data Recovery & Analysis | * การกู้คืนไฟล์ที่ถูกลบ (File Carving) และการตรวจสอบ File Signature * การทำ Disk Imaging และการตรวจสอบ Integrity (Hashing) |
| 13:00 – 14:30 | Anti-forensics Detection | การตรวจหาการใช้เครื่องมือลบทำลายหลักฐาน (Wiping), การซ่อนข้อมูล (Steganography) และการทำ Timestomping , Encryption , File obfuscation |
| 14:45 – 16:00 | Metadata (การตรวจสอบข้อมูลเมทาดาตา) Log File Analysis (การวิเคราะห์ไฟล์เหตุการณ์) | การวิเคราะห์ Metadata ของไฟล์เอกสาร และการไล่ Timeline จาก Event Logs และ Registry เพื่อระบุพฤติกรรมผู้ใช้ |
📅 ตารางการอบรม Day 2: Advanced Fraud & Practical Workshop
วัตถุประสงค์: ประยุกต์ใช้เครื่องมือกับคดีทุจริตในองค์กรและสรุปผลการสืบสวน
| เวลา | หัวข้อหลัก | รายละเอียดและมาตรฐานที่เกี่ยวข้อง |
| 09:00 – 10:30 | การสืบสวนภัยคุกคามจากคนในและการรั่วไหลของข้อมูล (Insider Threat & Data Leak Investigation) | การตรวจสอบการรั่วไหลของข้อมูล และการติดตามพฤติกรรมพนักงานที่มีความเสี่ยง |
| 10:45 – 12:00 | Corporate & Financial Fraud & Intellectual property infringement | เทคนิคการสืบสวนการยักยอกเงิน และการละเมิดทรัพย์สินทางปัญญาช่องทางดิจิทัล |
| 13:00 – 14:30 | การสืบสวนนิติวิทยาศาสตร์บนอุปกรณ์เคลื่อนที่ (Mobile Forensics Investigation) | * การเก็บหลักฐานจากสมาร์ทโฟน การวิเคราะห์ข้อมูล แอปแชท และพิกัดตำแหน่ง (GPS) |
| 14:45 – 16:00 | Testifying in Court (กระบวนการเบิกความและนำเสนอพยานหลักฐานในชั้นศาล) Hands-on Workshop & Investigation Report Writing (เทคนิคการเขียนรายงานผลการสืบสวนสอบสวน) | Lab: จำลองคดี “ไฟล์ลับหายไปและการรั่วไหลของข้อมูล” * การเขียนรายงานสรุปผล (Forensic Report) ให้ผู้บริหารและฝ่ายกฎหมาย |

หลักสูตร Computer Forensics Exam Mastery: 1-Day Intensive Bootcamp (พร้อม Voucher สอบ)
หากคุณกำลังมองหาคอร์ส อบรม Computer Forensics ที่กระชับ ตรงประเด็น และเน้นผลลัพธ์ในการสอบใบรับรอง หลักสูตร “Computer Forensics Exam Mastery: 1-Day Intensive Bootcamp” คือคำตอบสำหรับคุณ
นี่คือหลักสูตรที่ออกแบบมาเพื่อ “เตรียมความพร้อมก้าวสู่ความเป็นมืออาชีพด้าน Digital Forensics” พร้อม Voucher สำหรับการสอบ เพื่อให้คุณพร้อมทั้งความรู้และโอกาสในการคว้าใบรับรอง
? เป้าหมายของหลักสูตร
- เข้าใจกระบวนการ เพื่อให้ผู้เรียนเข้าใจกระบวนการทางกฎหมายและเทคนิค Digital Forensics ที่ออกสอบบ่อย
- วิเคราะห์เป็น เพื่อฝึกฝนการวิเคราะห์โจทย์
- มั่นใจก่อนสอบ เพื่อทบทวนเนื้อหาและสร้างความมั่นใจ
? จุดเด่น
- Expert Instructor: สอนโดยผู้เชี่ยวชาญที่มีประสบการณ์จริงด้าน Digital Forensics และได้รับการรับรองทักษะการสอน
- Exam-Focused: เนื้อหาถูกออกแบบมาเพื่อการสอบโดยเฉพาะ ไม่เสียเวลากับทฤษฎีที่ไม่จำเป็น
- Cheat Sheet Included: แจกสรุป Keyword และ Path สำคัญที่ต้องจำ ช่วยลดเวลาในการอ่านหนังสือเอง
กลุ่มเป้าหมายของหลักสูตร ” Computer Forensics Exam Mastery: 1-Day Intensive Bootcamp ” ดังนี้:
- The Auditors และ Compliance Officers
- IT Managers และ ผู้เชี่ยวชาญด้านความปลอดภัย IT (Security Experts)
- นักสืบสวนทางนิติวิทยาศาสตร์ดิจิทัล (Digital Forensic Investigators)
- เจ้าหน้าที่บังคับใช้กฎหมาย
- ผู้ที่กำลังเตรียมสอบใบรับรอง (Certification Seekers)
? กำหนดการอบรม (Detailed Schedule)
09:00 – 12:00: High-Yield Theory Summary
ช่วงเช้าเน้นปูพื้นฐานและสรุปหัวข้อที่ออกสอบบ่อย (High-Frequency Topics)
09:00 – 10:00: Legal & Process Foundation
- The Four Principles: สรุปหลักการ 4 ข้อของพยานหลักฐานดิจิทัล (ACPO Guidelines)
- Evidence Handling: ขั้นตอนที่ถูกต้องในการเก็บหลักฐาน (Seizing) และการทำ Chain of Custody
- Admissibility: ปัจจัยสำคัญที่ศาลใช้พิจารณาความน่าเชื่อถือของพยานหลักฐาน
10:00 – 10:15: พักเบรก Morning Break
10:15 – 11:15: Technical Forensics Deep-Dive
- Acquisition Techniques: เจาะลึกความต่างระหว่าง Static vs. Live Acquisition (Bit-stream image vs. Backup)
- Windows Artifacts Mastery: ชี้เป้า “จุดตาย” ที่ต้องรู้ใน Registry, Link Files และ Shellbags
- Event Logs & USB: เทคนิคการแกะรอยการเข้าถึงระบบและการเชื่อมต่ออุปกรณ์ภายนอก
11:15 – 12:00: Specialized Areas Briefing
- Network & Web Forensics: การวิเคราะห์ Log (Log Analysis)
- Email & Mobile Forensics: ลำดับขั้นตอนการสืบสวน (Investigation Flow)
13:00 – 16:00: Exam Drill & Strategy
ช่วงบ่ายเปลี่ยนความรู้เป็นคะแนน ด้วยการฝึกทำโจทย์เสมือนจริง
13:00 – 14:30: Domain-Based Practice (Set 1)
- ฝึกทำโจทย์แยกตามหัวข้อ (Legal, Windows, Network, Cloud)
- วิเคราะห์โจทย์ เจาะลึก ให้ดูว่า “คำถามนี้ถามหาอะไร”
14:30 – 14:45: พักเบรก Afternoon Break
14:45 – 15:45: Final Mock Exam (Full Speed)
- จำลองการสอบจริงพร้อมเทคนิคการตัดตัวเลือก (Elimination Technique)
15:45 – 16:00: Q&A and Exam Readiness Tips
- ถาม-ตอบ และเคล็ดลับเตรียมตัวก่อนเข้าห้องสอบ
ข้อมูลการสมัคร (Enrollment Info)
- วันและเวลา: 9.00-16.00
- สถานที่: Onsite อาคาร Bangkok Business Center (สุขุมวิท 63 หรือซอยเอกมัย) or In house Training สำหรับองค์กร
- ราคา: 16,500 บาท (ยังไม่รวม VAT) ราคานี้รวม Voucher สอบ + LMS เรียบร้อยแล้ว
- ช่องทางลงทะเบียน LINE ID: orionforensics หรือ https://line.me/ti/p/gXyoCB99cG
- ช่องทางลงทะเบียน Email:

หมายเหตุ
- ทุกหลักสูตรสามารถจัดในรูปแบบ ( In-House) อบรมในองค์กรได้ โปรดติดต่อ Email:

- สิทธิประโยชน์ทางภาษี: ค่าใช้จ่ายจากการอบรมสามารถนำไปลดหย่อนภาษีได้ 200% (พระราชบัญญัติส่งเสริมการพัฒนาฝีมือแรงงาน พ.ศ. 2545)
- หลักสูตรภาคปฏิบัติผู้เข้าอบรมต้องเตรียมคอมพิวเตอร์มาเอง
- ในกรณีอบรม ณ ห้องอบรมบริษัทลูกค้า ค่าอบรมจะไม่รวมค่าอาหารกลางวัน และอาหารว่าง 2 มื้อ
- หลักสูตรอาจมีการเปลี่ยนแปลงวันเวลาจัดอบรมตามความสะดวกของลูกค้า


Digital Forensics (นักสืบไซเบอร์) คือสิ่งจำเป็นในยุคนี้
โลกดิจิทัลที่ “เร่งรีบ” ไม่แพ้กรุงเทพฯ
ทำไมทักษะ Digital Forensics (นักสืบไซเบอร์) คือสิ่งจำเป็นในยุคนี้
สวัสดีครับ! ในฐานะคนที่คลุกคลีอยู่กับโลกของ Digital Forensics (การสืบสวนพยานหลักฐานดิจิทัล) ผมอยากชวนคุณคุยเรื่องหนึ่งครับ
ทุกวันนี้ เราใช้ชีวิตกันแบบ “เร่งรีบ” ในกรุงเทพฯ ใช่ไหมครับ? ทุกอย่างคือการแข่งขัน แย่งกันขึ้น BTS วางแผนหนีรถติด ข้อมูลข่าวสารวิ่งเข้าหาเราทุกวินาที
โลก “ดิจิทัล” หรือโลกออนไลน์ของเรา ก็ไม่ต่างกันเลยครับ มันคือกรุงเทพฯ อีกเวอร์ชันหนึ่ง ที่ทั้งเร็ว เร่งรีบ และเต็มไปด้วย “ข้อมูล” (Data) มหาศาล
เปรียบเหมือน “รถ” ที่วิ่งกันขวักไขว่
แต่คำถามคือ ถ้าเกิด “อุบัติเหตุ” หรือ “ภัยคุกคามทางไซเบอร์” (Cyber Threats) ขึ้นล่ะ? เราจะ “เคลียร์” ปัญหานั้นยังไง?

? ชนแล้วหนี
- ในชีวิตจริง คุณจอดรถไว้ในซอย กลับมาอีกที ไฟท้ายแตก มีรอยบุบ แต่… ไม่มีคนเห็น ไม่มีโน้ต กล้องวงจรปิดก็ดันชี้ไปอีกทาง คุณหัวเสีย แต่ไม่รู้เลยว่าใครทำ ทำตอนไหน
- ในโลกดิจิทัล มันเหมือนกับที่คุณเปิดคอมมาแล้วพบว่า… ไฟล์ถูกลบ (Deleted Files) หายไปเฉยๆ, โปรแกรมไม่ทำงาน หรือแย่กว่านั้นคือ บัญชีโดนแฮ็ก (Hacked Account) คุณรู้ว่า ‘มีอะไรผิดปกติ’ แต่ไม่รู้ว่าใครทำ? มันเข้ามาทางไหน? และไฟล์ที่หายไปจะทำ การกู้ข้อมูล (Data Recovery) กลับมาได้ไหม?
Digital Forensics เปรียบเหมือน “ทีมสืบสวนที่เกิดเหตุ” ครับ
ต่อให้คนร้ายคิดว่า “ลบ” ไปแล้ว เราคือคนที่จะไปไล่หา ‘ร่องรอยดิจิทัล’ (Digital Footprints) ที่ทิ้งไว้ เราจะสอนให้คุณเป็น ‘นักสืบ’ ที่สามารถตามหาหลักฐาน และเรียนรู้กระบวนการ Data Recovery เพื่อ ‘กู้’ ไฟล์ที่คิดว่าหายไปแล้วกลับมา และ ‘ปะติดปะต่อเรื่องราว’ ว่าเกิดอะไรขึ้นกันแน่ นี่คือหัวใจของ การสืบสวนทางดิจิทัล ครับ
?️ ท่อประปาแตก
- ในชีวิตจริง คุณเคยเห็นถนนทรุด หรือน้ำท่วมขังแบบไม่ทราบสาเหตุไหมครับ? กว่าเราจะรู้ตัว “ท่อประปา” ที่อยู่ใต้ดินก็อาจจะ ‘รั่ว’ ไปนานแล้ว สร้างความเสียหายเป็นวงกว้าง เรามองไม่เห็นปัญหา จนกระทั่งมัน ‘โผล่’ ขึ้นมาบนผิวถนน
- ในโลกดิจิทัล นี่คือปัญหาคลาสสิกของ “ข้อมูลรั่วไหล” (Data Breach หรือ Data Leak) ครับ มันอาจเกิดจากพนักงาน (ทั้งตั้งใจหรือไม่ตั้งใจ) แอบส่งข้อมูลสำคัญของบริษัทออกไปทีละเล็กทีละน้อย หรือมี ‘ช่องโหว่’ ที่เรามองไม่เห็น ทำให้ข้อมูลสำคัญ ‘รั่ว’ ออกไปหาคู่แข่ง กว่าเราจะรู้ตัว ความเสียหายก็อาจจะประเมินค่าไม่ได้แล้ว
Digital Forensics เปรียบเหมือน “เครื่องมือตรวจสอบ” ครับ
แทนที่จะรอให้ถนนพัง เราจะสอนให้คุณใช้เครื่องมือเพื่อ ‘ตรวจสอบ’ และ ‘ฟังเสียง’ ที่ผิดปกติ เราสามารถ ‘อ่านแผนที่’ (หรือ Log file) เพื่อดูว่า ‘ข้อมูล’ ของเราวิ่งไปทางไหนที่มันไม่ควรไป หรือใครเป็นคนแอบมา ‘เจาะท่อ’ ของเรา นี่คือทักษะสำคัญสำหรับ Cyber Investigation เพื่อหยุดยั้งความเสียหายก่อนที่มันจะสายเกินไป

? ทำไมทักษะนี้ถึงเป็น “ข้อได้เปรียบ” ในยุคแห่งการแข่งขัน?
ในโลกธุรกิจที่ “แข่งขัน” กันสูงเหมือนแย่งที่จอดรถในห้างวันเสาร์ การ “รู้ทัน” และ “ปกป้อง” ข้อมูลได้ คือความได้เปรียบมหาศาล
คุณไม่จำเป็นต้องเป็น “เทพคอมพิวเตอร์” หรือมีพื้นฐาน Cybersecurity (ความปลอดภัยทางไซเบอร์) มาก่อน
คุณแค่ต้อง “อ่านแผนที่” ให้ออก และ “รู้จักเครื่องมือ” ที่ถูกต้อง
เมื่อคุณมีทักษะ Computer Forensics นี้:
- สำหรับเจ้าของธุรกิจ: คุณจะรู้ทันทีเมื่อมีภัยคุกคาม ,สงสัยว่ามีการทุจริตภายใน, พนักงานขโมยข้อมูล หรือลบข้อมูล
- สำหรับคนทำงาน: ทักษะนี้คือ “อาวุธลับ” ที่ทำให้คุณโดดเด่น ไม่ว่าคุณจะอยู่ฝ่าย IT, HR, หรือกฎหมาย คุณจะกลายเป็นคนที่ช่วย “ไขปริศนา” ที่คนอื่นแก้ไม่ได้ (ถือเป็น ทักษะ IT ที่มีมูลค่าสูงมาก)
- สำหรับคนทั่วไป: คุณจะเข้าใจโลกดิจิทัลมากขึ้น ปกป้องตัวเองและครอบครัวจากภัยออนไลน์ได้ดีขึ้น, ตรวจสอบเว็ปไซต์ปลอม, เว็ปหลอกลวง, อีเมลหลอกลวง หรือตรวจสอบไฟล์อันตราย
? คุณก็เริ่มต้น “เรียน Forensics” ได้ แม้ไม่มีพื้นฐาน
ผมเชื่อว่าหลายคนอ่านถึงตรงนี้แล้วอาจจะคิดว่า “มันคงยาก” หรือ “เราไม่มีพื้นฐานเลย”
นั่นคือเหตุผลที่ผมออกแบบ หลักสูตร Digital Forensics มาครับ และมันถูกออกแบบมาเพื่อ “คนธรรมดา” ที่อยากเปลี่ยนความ “ไม่รู้” ให้เป็น “รู้จริง”
นี่คือคอร์ส อบรม Computer Forensics ที่เราจะข้ามศัพท์เทคนิคที่น่าปวดหัว แต่เน้น “กระบวนการ” และ “วิธีคิด” ที่คุณเอาไปใช้ได้จริงทันที
ถ้าคุณเป็นคนหนึ่งที่อยาก “อ่านเกม” ในโลกดิจิทัลให้ออก อยากมี “ทางลัด” เข้าใจร่องรอยที่คนอื่นมองไม่เห็น…
ผมอยากชวนคุณมาเริ่มต้น “ก้าวแรก” ด้วยกันครับ

ลองดูรายละเอียด หลักสูตร Digital Fraud Investigation Techniques ของเราได้ที่นี่ครับ
แล้วมาเปลี่ยนความ “สับสน” ในโลกดิจิทัล ให้เป็น “อาวุธ” ที่ทรงพลังที่สุดของคุณกันครับ
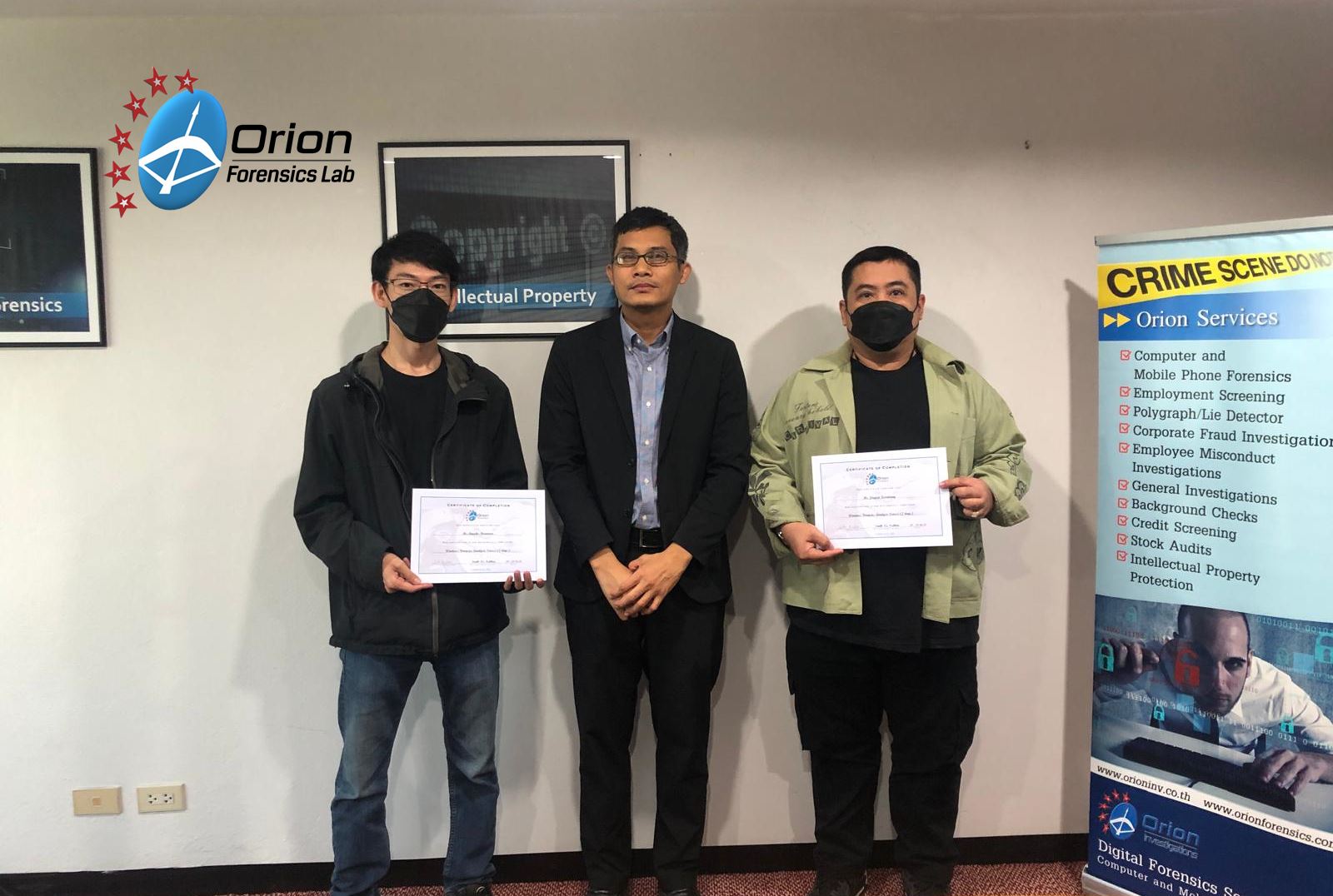
Hands on Workshop Windows Forensics Analysis Course 2 Day
Orion Forensics has organized training course Hands-on Workshop Windows Forensics Analysis Course 2 Day on 24 – 25 December 2024.
A 2-day practical training course for Cyber security and Blue team who are responsible for digital forensic investigations & forensic digital examinations. responsible for extracting and analyzing data from digital devices.
- The course is aimed for people wishing to become digital forensic investigators or wishing to update their forensic skills.
- The course is designed by digital forensic experts with many years’ experiences both domestically.
- The training provides a solid foundation in Windows Forensics techniques reinforced by practical hands-on exercises using a wide range of free and open-source forensic tools.
In-House \ On-Site Training available -please contact sales directly at forensics@orionforensics.com







Cryptocurrency Investigations and Tools

If you believe you may have been a victim of a cryptocurrency scam and need to gather evidence to support a police complaint, Orion Investigations may be able to help.
A cryptocurrency blockchain is a decentralized public digital ledger that exists across a network which contains details of cryptocurrency transactions.
In order to conduct investigations, Orion’s Director of Computer Forensics Services Andrew Smith has developed Blockchain Detective, an investigation tool that simplifies the downloading of cryptocurrency transactions. It automatically generates a visual representation of the transactions (one node per unique address) making it easy to follow the flow of cryptocurrency from one address to the next and automatically identifies exchange addresses.
If you have become a victim of a crypto scam, contact Orion to see how we can assist.
Read full article ==> Cryptocurrency Investigations
Email : forensics@orionforensics.com
Line ID : orionforensics
Mobile Phone : +66(0)89-960-5080

Responding to a RANSOMWARE ATTACK
Responding to a RANSOMWARE ATTACK
When a company becomes a victim of a ransomware attack they will often contact Orion to ask if we can recover their encrypted data. In almost every case the answer is going to be no as we will not have access to a recovery key to decrypt the data. Therefore, it is vital that the company maintains up to date backups of their data.
The number of ransomware attacks continue to rise year on year. According to the Verizon 2022 Data Breach Investigation Report there was a 13% increase in ransomware attacks and ransomware was involved in 25% of all breaches.
One of the trends now employed by the attackers is the double extortion method. The attackers gain access to the network and steal the confidential data. They will then encrypt the data on the network and demand a ransom to be paid to decrypt the data. If the victim has the data backed up and refuses to pay the ransom, the attackers will then threaten to release the data online.
When a company falls victim to a ransomware attack the natural response is to wipe the infected machine and restore the data in order to get up and running again as quickly as possible. As a result, attackers will often use ransomware as a way to destroy any evidence of a data breach after they have extracted the data from the network.
It is therefore important for the company to conduct a thorough investigation even if the encrypted data cannot be recovered.
The purpose of the investigation is to preserve potential evidence in order to:
- Identify how the system came to be infected with ransomware
- Identify if any confidential data has been extracted from the system
- Provide answers to the regulatory authorities and show you have taken reasonable steps to prevent a repeat
- Preserve the data in case decryption keys are released at a later date
If you become a victim of a ransomware attack, how should you respond?
- Do not shut down the infected devices
- Disconnect the infected devices from network
- Preserve logs such as Firewall, VPN, anti-virus logs or any other logs which can be saved
- Document all information pertaining to the ransomware attack
- Photo or copy of the ransom demand note/splash screen
- Ransomware variant name if known
- The file extension of encrypted files
- The date and time of the attack
- The file naming scheme for the ransom note/readme file left by attacker
- Any email addresses or URL or other method provided by the attacker for communications
- Required payment method/bitcoin addresses provided by the attacker
- Ransom amount demanded if known
What information will the investigators need to know from you?
- Number of devices affected
- Type of devices, make, model, size of hard drive
- What OS is on the devices
- Is there encryption on devices and If so what encryption and can IT provide a recovery key?
- Location of devices
- Timeline of events
- Details of ransomware
It is important to respond quickly and get the investigators onsite as soon as possible so that they can begin the process of preserving potential evidence from the infected devices. This will include not only the data from the hard drives and logs but also volatile data such as RAM memory which can provide a wealth of information such as network connections, open ports and destination IP addresses.
We would therefore recommend that you do not wait until you become a victim of a ransomware attack before deciding which investigation company you wish to work with. Do your research, due diligence and complete the vendor onboarding process before an attack occurs. This will ensure a quick response and prevent the loss of any potential evidence.
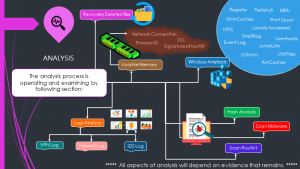
The Analysis Process Infographic
The Article provided by – Andrew Smith – Director of Computer Forensics Services
Email : forensics@orionforensics.com
Line ID : orionforensics
Mobile Phone : +66(0)89-960-5080
Download Article => RESPOND TO A RANSOMWARE ATTACK
vc_column_text]

Hands-on Workshop |Digital Forensics Foundation Course 4 Days Organized by Tech Direct Co., Ltd.
Orion Forensics has organized training course Hands-on Workshop Digital Forensics Foundation Training Course – 4 DAYS on 20th – 23rd December 2022
Tech Direct Co., Ltd. organized the Hands-on Workshop Digital Forensics Foundation Training Course – 4 DAYS on 20th – 23rd December 2022.
A 4-day practical training course for National Intelligence Agency Thailand and police who are responsible for digital forensic investigations.
- The course is aimed for people wishing to become digital forensic investigators or wishing to update their forensic skills.
- The course is designed by digital forensic experts with many years’ experiences both domestically and internationally.
- The training provides a solid foundation in forensic principles and techniques reinforced by practical hands-on exercises using a wide range of free and open-source forensic tools.

The In-House \ On-Site Training available -please contact Digital Forensics Team directly at forensics@orionforensics.com





Orion Forensics Investigations Participated in Cyber Defense Initiative Conference (CDIC) 2022
On November 9-10, 2022, Orion Forensics Investigations Participated in the Cyber Defense Initiative Conference CDIC 2022 at the BITEC Exhibition and Convention Center.
CDIC is the largest cybersecurity conference and presentation in Thailand.
There were many government and private sectors participating in the meeting.
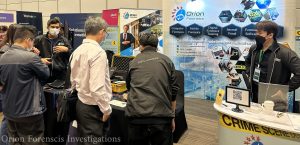

Organizing this event The presentation under the theme
“Optimizing Security of Things and Digital Supply Chain Risk”
The event is important in enhancing security potential in various areas such as;
- The Importance of empowering cybersecurity for connected IoT devices
- Risk management in the digital information
- Blockchain, AI-powered, Quantum technology advancements are applied both positively in defense and negatively in attack.
- Major changes to the new version of ISO/IEC 27002 include the “Information Security, Cybersecurity & Privacy Protection” controls for ISO/IEC 27001 (ISMS) certification organizations to know when implementing them.
- Promulgation of law Cyber Security Act and Personal Data Protection Act, Etc.

Over two days, Orion Forensics Investigations participated in the event as set up booth, give away prizes to attendees and discuss Digital Forensics Services and Digital Forensics Training Courses, as well as build relationships with other cybersecurity leaders in attendance.
Although, Orion Forensics Investigations has brought and presented sample of equipment in work – related in Digital Forensics, both in terms of software and hardware for study and experiment purposely.

Read More

Hands-on Workshop |Digital Forensics Foundation Course 4 Days to GrowPro Consulting & Services Co.,Ltd.
Orion Forensics LAB has organized training course On-Site| hands-on Workshop Digital Forensics Foundation Training Course (4 DAYS) for GrowPro Consulting & Services Co.,Ltd. on 6th – 9th September 2022
A 4 day practical training course for people who are responsible for digital forensic investigations or are wishing to become a digital forensic investigator. The course will provide a solid foundation in the understanding of digital forensics principles and techniques. Each subject is covered in depth and supported by practical scenario based exercises to reinforce the learning points.
As required from expertise, Orion Forensics lab had adapted the curriculum to meet the professional workload of Cloud data collection, Malware Analysis and the Volatility Framework to analyze RAM Memory.
Hands-on Workshop Digital Forensics Foundation Training Course (4 DAYS) Digital Forensics Foundation Training Course 4 Days



In-House \ On-Site Training available -please contact sales directly at forensics@orionforensics.com
][/vc_row]</p>
Read MoreOffences according to the 2007 Computer Crime Act , Judgement of the Supreme Court 2600/2563
Offences according to the 2007 Computer Crime Act section 3 and 7, Judgement of the Supreme Court 2600/2563”A case study of an ex-employee who illegally accessed their company email account after have resigned from the company
Read More






