
Corporate Fraud and Covid-19
Fraud is an intentional act to deprive another of property or money by guile, deception, or other unfair means. Corporate fraud is fraud against a company and can be committed by internal or external parties. Internal fraud is when an employee, manager, or owner commits fraud against their own company such as theft or misuse of company assets. External fraud is committed by third-parties and includes bribery, corruption, hacking, theft and insurance, loans and payment frauds.
It is estimated that organizations globally lose 5 percent of gross revenue to fraud.
A general understanding of human nature and crime may lead us to believe that corporate fraud is committed by employees with bad intentions and a faulty moral compass. However, fraud experts, after analyzing thousands of cases of corporate fraud, have found that other factors are more important in leading an employee to commit fraud.
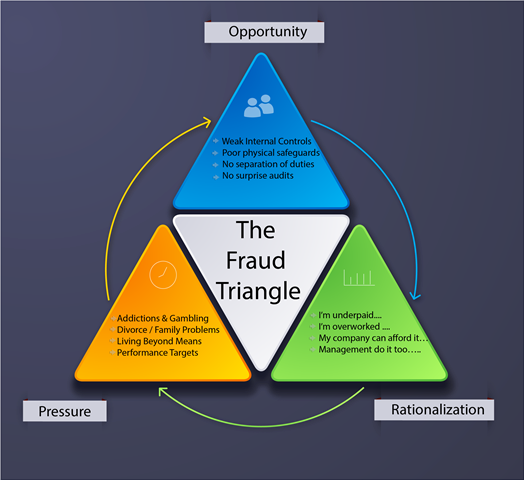
These factors are illustrated in the Fraud Triangle. The Fraud Triangle consists of Opportunity, Pressure, and Rationalization. To take a simple example – The petty cash draw in Jack’s company is never locked, is not monitored, and is never reconciled. He has an Opportunity. He is low on cash, it is his girlfriend’s birthday and he has not bought a present yet. He has Pressure. A few hundred dollars will not harm the company, nobody will find out, he is underpaid, and overworked and his boss is an idiot. He now has Rationalization and all three boxes are ticked for Jack to become a corporate fraudster, despite being a generally ethical and well-intentioned employee.
How can the Fraud Triangle help us understand the threat of fraud during the Covid-19 pandemic?
Opportunities – while working from home, many companies have had to quickly introduce new work-processes with fewer controls. Pressure – we all know the pressure faced by many during the pandemic due to uncertainties, reduced salaries, family crises and general anxiety levels. Rationalization – while working from home, employees may feel less connected to their employer and colleagues or they may feel dissatisfaction with their employer for measures taken during the pandemic, such as salary reductions or redundancies, making it easier for them to justify committing fraud.
The Association of Fraud Examiners (ACFE) – the world’s largest anti-fraud organization and provider of anti-fraud training and education (and the source of most of the statistics presented in this article) – has observed a significant increase in fraud as a result of Covid-19. Especially in employee embezzlement, cyber fraud, payment fraud and identity theft caused by less oversight due to remote workforces. ACFE members also report challenges to investigating fraud due to travel restrictions and other lack of access to evidence.
While Covid-19 may have created new opportunities and different kinds of fraud, the fundamentals of fraud and how companies can protect themselves from fraud remain the same. The following are some of the key tools available to companies to reduce the risk of being victims of fraud –
- Hotlines – 43 percent of frauds are detected through tips. Organizations with hotlines detect fraud sooner and limit their losses. This illustrates the importance of having a clear reporting mechanism for employees, suppliers, and others to report suspicions of fraud. Most fraudsters are not saving for a rainy day – they tend to live beyond their means and colleagues may pick up on this and report their suspicions. Other red flags of fraud include financial difficulties, unusually close relationships with vendors/customers and addictions.
- Fraud Awareness Training – Employees are more likely to provide tips after they have received training on fraud. They are also less likely to commit fraud if they are aware of the company’s code of conduct and anti-fraud policies and internal controls. Topics will include red flags of fraud, types of fraud, and fraud reporting processes.
- Tone at the Top – Many factors in the Rationalization of a fraud involve poor management. Management and owners must set an example in terms of ethical behaviour and fair treatment of employees and vendors.
- Incident Response Plans – Companies should have a plan in place for how they will respond to fraud or allegations of fraud. This may include identifying external resources that can be called upon to support investigations and legal actions. Once fraud is detected, it is important to collect evidence in a forensically sound manner so it can be used in legal proceedings if necessary. Evidence should also be carefully reviewed before deciding whether legal action can be taken against the fraudsters. Companies often rush to confront a fraudster before sufficient evidence has been gathered to strengthen the company’s position.
- Internal Controls – Most companies will not have the open Petty Cash drawer that helped corrupt poor Jack, but many have comparable vulnerabilities that employees will become aware of over time. Having tighter internal controls including separation of duties, physical safeguards, and surprise audits will reduce the Opportunity factors in the fraud triangle. Many external auditors will also provide internal control review services.
- Fraud Risk Assessments – This involves proactively identifying and mitigating the company’s vulnerabilities to internal and external fraud. It can be done internally or with the support of outside consultants.
- External Audits – External audits of financial statements are also a significant source of fraud discoveries, especially in larger organizations. Identifying potential frauds should be included in the scope of engagement with external auditors.
- Pre-Employment Screening – These include checking of past employment duties, criminal and background checks, educational verification, and reference checks. Organizations should ensure that their employment screening processes comply with data protection laws, with no unauthorized accessing of applicants’ data, and consider the use of a professional screening company.
As the saying goes, prevention is better than cure. Implementing these anti-fraud tools will reduce the risk of your organization becoming a victim of fraud. It will also ensure that, if you do become a victim of fraud, the response will be swift and appropriate, and the damage will be limited.
Author : Peter Holmshaw – Managing Director at Orion Investigation Co.,Ltd.
Read MoreEMAIL BANK TRANSFER FRAUD (BEC) – AVOID BECOMING A VICTIM
We have seen a significant increase in the number of cases where employees responsible for issuing payments on behalf of the company have been tricked into transferring the money into bank accounts under the control of a malicious person (Business Email Compromise). Already in the first 13 days of this year (2022) we have been contacted in relation to three such cases.
How is this type of fraud achieved and what can you do to prevent your company becoming another victim of fraud via email?
The fraudster will can often gain unauthorized access to an email chain via a number of ways. This includes
- Hacking the company network or your vendor’s network
- Unauthorized access by a malicious employee
- Using social engineering or phishing emails
- Using email login details that have become compromised for example by malware located on the computer system or the user using an unsecured WIFI network without a VPN
It should be noted that it is often very difficult to identify how the actual compromise has occurred.
Having gained access to the email chain the fraudster will then create an email address that looks almost identical to an email address within the chain that should be receiving a payment. They will then send an email from the fake email address using an excuse such as “our bank account is being audited so you need to make the payment into this other account of ours”. They will often then follow up with several more emails pushing for the payment to be made as quickly as possible. By using a fake email address, they have now taken control of the conversation. Most victims fail to notice the slight differences between the real email address and the fake one. As a result, all further emails are being diverted away from the intended real recipient to the fraudster. Once the payment has been made it will be extremely difficult to get the money back so prevention is the best policy.

If you do find yourself in the unfortunate position of having been a victim of this type of fraud, then Orion may be able to assist in gathering evidence and preparing the evidence so you can report the crime to the police. It is important to take the following steps.
- Retain an electronic copy of all original emails in the email chain and especially the emails requesting payment to a new bank account and any follow up emails from the fraudster.
It is important to keep an electronic copy of the original received emails and not ones that have been forwarded on internally to other staff members. The reason for this is that the emails contain embedded hidden information that is not usually seen when looking at the email through an email client. This information is known as email header information and contains details of all the computers the email has passed through from the sender to the recipient.
The email header will also contain time and date information and possibly the originating Internet Protocol (IP) address of the sender. In order for a device to connect to the Internet it has to be allocated an IP address. This IP address will be allocated to the customer by an Internet Service Provider (ISP).
Therefore, if we can identify the originating IP address of the email and the time and date information we can identify which ISP is responsible for allocating the IP address and from which country. Law enforcement can then make a legal request to the ISP for details of who the IP address was allocated to at the time and date the email was sent.
When you forward the emails internally the original email header information can be lost which is why it is important to preserve the original emails received in an electronic format.
Case Studies – Examples of cases where we have been able to assist our clients.
Example 1 – A Thai company asked us to examine the emails received from the fraudster to try and identify if they had been compromised or their USA vendor. We were able to show that the fraudster had used the USA vendor email login details to log into the email account via webmail from Nigeria and as a result it was the vendor who had been compromised.
Example 2 – A fraudster had created fake email addresses very similar to our client’s legitimate email addresses to commit the fraud. As a result, the other company concluded our client’s network had been compromised and they then took our client to court to sue for failing to maintain a secure computer network. Based on the evidence available it was impossible for the other company to draw this conclusion. Orion went to court as the expert witness for our client stating that based on all available evidence at the time it was impossible to conclude how the breach to the email system had occurred and which company had been compromised.
If you need assistance, then please do not hesitate to contact Orion Forensics to see how we may be able to help.
Read More
