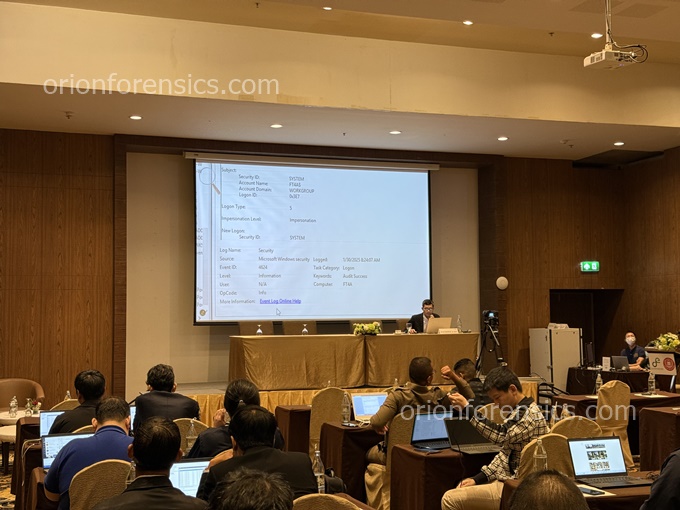
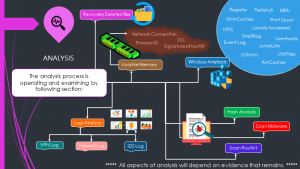
When Cyber Threats pose dangers and Cyber Awareness may no longer be sufficient, Digital Forensics has become an essential skill that everyone should know. This knowledge helps understand techniques and best practices for investigating and finding digital forensic evidence, as well as the ability to understand, manage, and preserve critical and comprehensive Digital Evidence for use in legal proceedings.
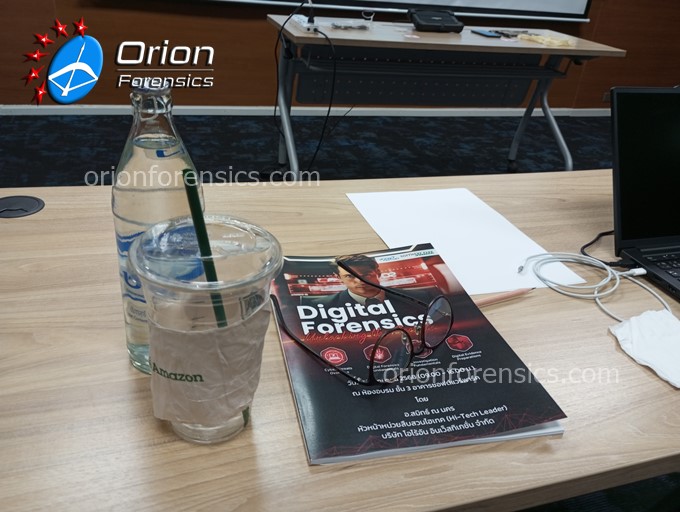
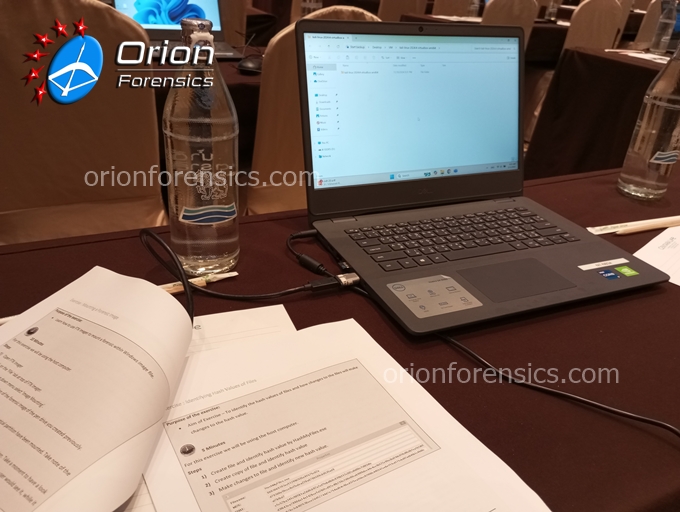
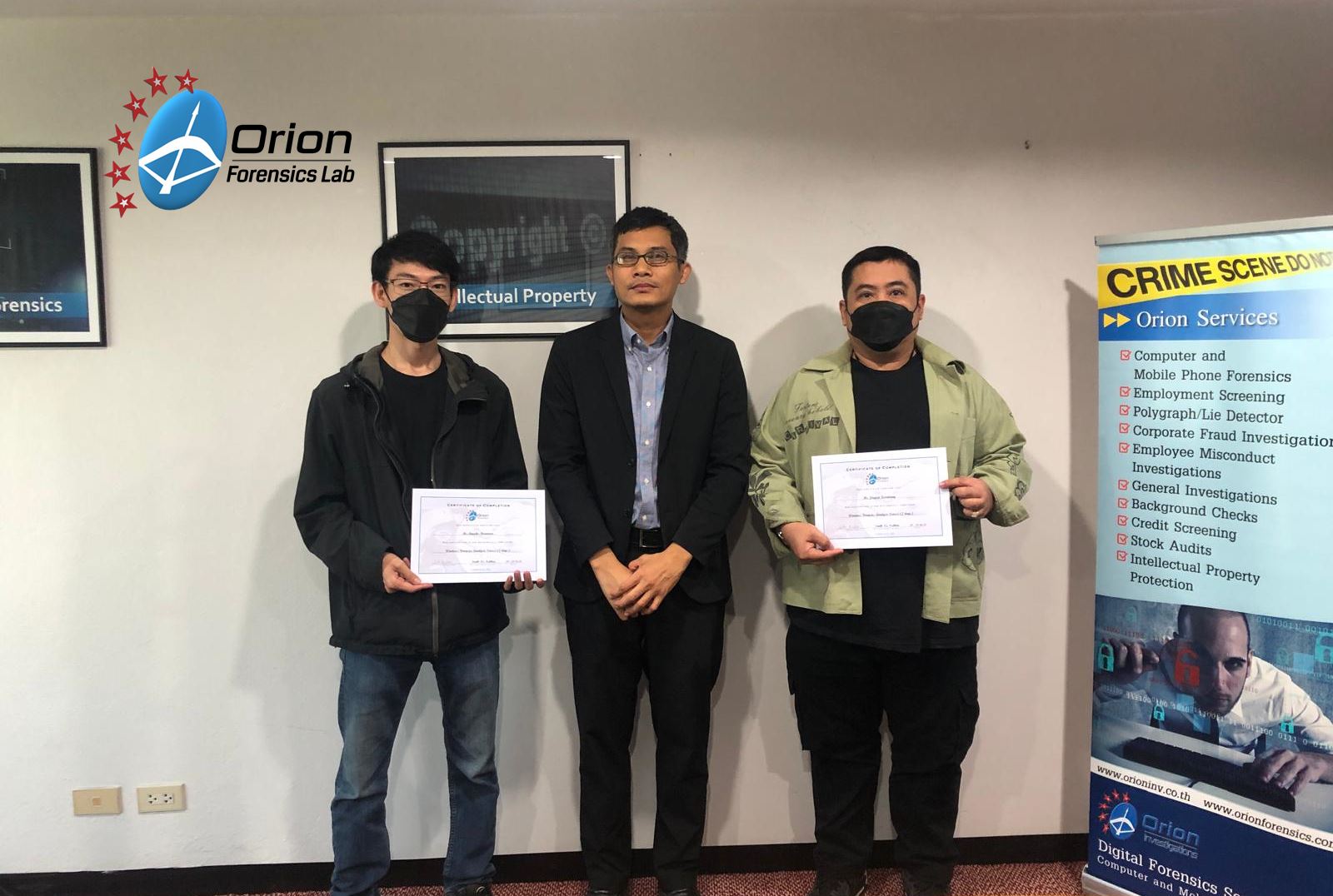
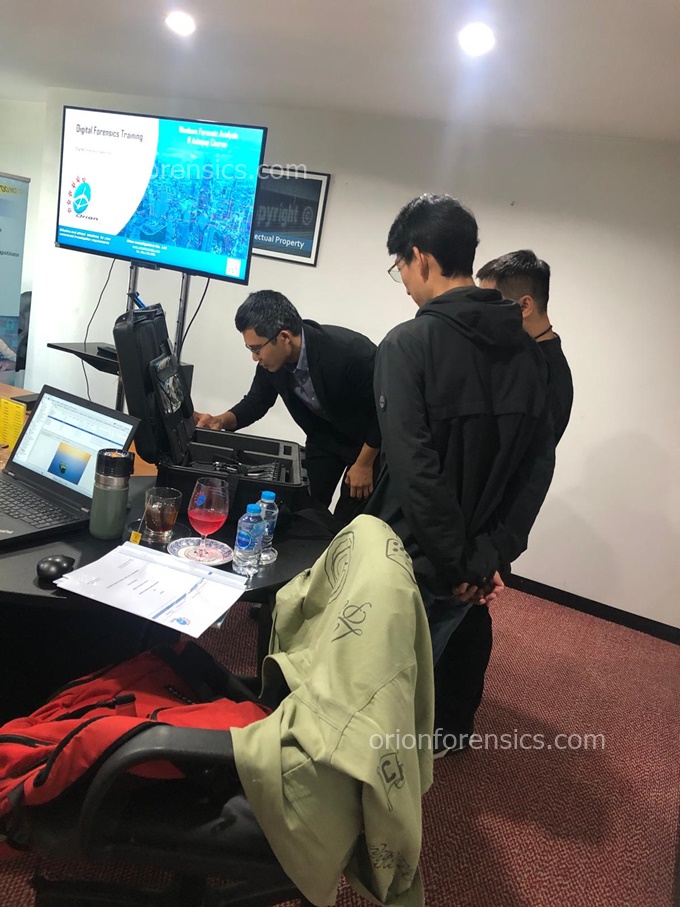
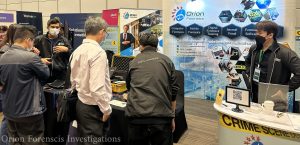
Atmosphere from Orion Forensics Lab in collaboration with Software Park Thailand organizing training on the topic “Digital Forensics Training Course – Unlocking the Secrets” on June 16, 2025, from 09:00-16:00 at Software Park Building, Chaeng Watthana Road, Nonthaburi Province. This training featured demonstrations of Mobile Forensics equipment for digital data extraction from mobile devices. Participating in this training will help attendees gain knowledge and understanding of Digital Forensics in various aspects (such as skills, techniques, and demonstrations of tools for collecting and preserving electronic data for use as Digital Evidence).